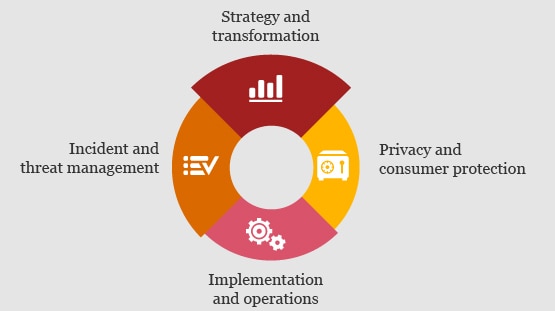
Strategy and transformation
Strategy and transformation: growth through new technologies
Many organisations are pursuing emerging technologies to develop new products, services, or ways of doing business. However, companies don’t always consider the emerging cybersecurity threats that could impact these systems after they’re implemented. We can help you assess, manage and design transformation strategies to enhance your cybersecurity capabilities that will enable the business, sustain and simplify compliance, and build trust with stakeholders.
Our services:
- Strategy development and transformation
- Cybersecurity risk and governance
- Third party security risk management
- Emerging technology security
- Cloud security
Privacy and consumer protection
Privacy and consumer protection: build trust and spark growth
Companies face a growing patchwork of new data protection and privacy laws in different territories (particularly the EU). This creates doubts when using data, resulting in missed business opportunities or regulatory breaches through inappropriate use, leading to loss of trust. We can help you craft a privacy programme compliant with global data-privacy regulations that can help you use data with confidence to create value and enhance customer trust.
Our services:
- General Data Protection Regulation (GDPR)
- Personal data governance
- Privacy assessment
- Privacy transformation
Implementation and operations
Implementation and operations: integrate, manage and improve technologies
Leaders seek to focus on opportunities that move their business forward, yet they’re often mired by today’s urgent cybersecurity and privacy challenges. We can help you efficiently integrate new and existing technology systems into your business, as well as actively manage them to deliver continuous operational improvements and increase your cybersecurity investment.
Our services:
- Identity and access management
- Analytics and monitoring
- Data protection
- Enterprise security architecture
- Managed security solutions
Incident and threat management
Incident and threat management: identify, respond to and remediate threats
Leaders know they need to rapidly and effectively respond to threats, but many lack confidence in their plans. A clear view of the strengths and weaknesses in your incident response plan is the first step in preparing you to confidently manage a potential security incident. We can help detect, respond to, investigate and remediate threats across the incident-management life cycle. Our team can assist you to understand dynamic cybersecurity challenges, adapt and respond to risks inherent to your business ecosystem, and prioritise and protect the most valuable assets fundamental to your business strategy.
Our services:
- Incident readiness (Game of Threats)
- Incident response
- Threat management
- Information sharing